Introduction
US retail shrinkage reached $112.1 billion in 2023—representing 1.6% of total sales—according to the National Retail Federation. In the UK, customer theft alone hit a record £2.2 billion in the same year. The NRF documented a 93% increase in average shoplifting incidents from 2019 to 2023, with a further 18% spike in 2024 and violence during theft events rising 17%.
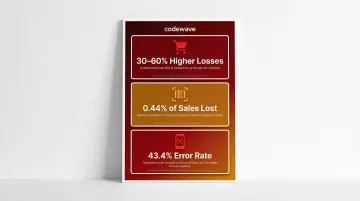
Traditional CCTV systems can't keep pace. They're designed for forensic review—useful for insurance claims after the fact, but incapable of stopping losses as they happen. Self-checkout lanes now process over half of all transactions in many stores, creating 30-60% higher losses than staffed checkout according to ECR Retail Loss research.
Layer in organized retail crime, employee safety hazards, and shrinking floor staff, and the structural vulnerability becomes hard to ignore.
Computer vision changes the equation. It processes live footage in real time, detecting theft, flagging safety hazards, and alerting staff before incidents escalate—rather than simply recording them for review afterward.
TLDR
- Computer vision detects suspicious behaviors and safety hazards in real time, unlike passive CCTV
- Self-checkout fraud detection catches scanning anomalies before transactions close
- Behavior-based detection sidesteps biometric facial recognition, reducing regulatory risk
- Edge computing keeps data on-premises and delivers alerts in milliseconds
- The same infrastructure prevents theft and workplace injuries, strengthening ROI across departments
The Hidden Cost of Retail Shrinkage (Why Traditional Systems Can't Keep Up)
Retail shrinkage encompasses four primary loss vectors:
- External theft (shoplifting and organized retail crime)
- Internal theft (employee and vendor fraud)
- Self-checkout errors and fraud
- Administrative mistakes
The balance has shifted — and the numbers show how far.
Self-checkout has become the highest-risk transaction point. ECR Retail Loss found that stores where 50% or more of transactions pass through self-checkout experience 30-60% higher losses than comparable stores. Non-scanning accounts for 0.44% of self-checkout sales and represents 9.5% of total store shrink. Under full random audit, Scan-and-Go mobile checkout showed a 43.4% error rate—meaning nearly half of all baskets contained some form of scanning discrepancy.
Traditional CCTV can't address this. It's a passive recording tool reviewed hours or days after incidents occur. Loss Prevention Magazine notes that even when incidents are clear, "assembling timelines, exporting video, and documenting evidence can consume hours per case." Staff manually scrub footage looking for what already happened—a forensic exercise, not a prevention strategy.
The staffing paradox compounds the problem. As retailers reduce floor staff and expand self-checkout to control labor costs, the ratio of unmonitored transactions climbs. Fewer eyes, more entry points, and higher transaction volumes create loss exposure that scales with store size even in well-run operations.
Theft isn't the only risk climbing undetected. Workplace safety is the second dimension most retailers underestimate. The Bureau of Labor Statistics reports 3.0 nonfatal occupational injuries per 100 full-time workers in retail, with slip-and-fall claims averaging $20,000 per incident. Blocked exits, spills, improper lifting, and aisle obstructions generate injury claims and regulatory liability that compound the cost of inadequate monitoring.
Legacy systems were built for documentation after the fact — not simultaneous, real-time detection across theft, fraud, and safety categories at once. That gap is exactly what computer vision is designed to close.
How Computer Vision Turns Cameras Into Intelligent Sensors
Computer vision software ingests video streams from standard IP cameras and processes frames using deep learning neural networks. Instead of storing raw footage for later review, the system generates structured data outputs—behavior flags, object classifications, anomaly scores, and alert triggers—in real time.
Edge Computing Drives Real-Time Response
Inference runs on edge compute appliances deployed within the store, not in the cloud. This architecture delivers two critical advantages:
- Millisecond-level alert latency: Staff receive notifications instantly, so intervention happens before transactions close or incidents escalate
- On-premises data processing: Raw video never leaves the store environment, reducing bandwidth costs and satisfying data residency requirements under GDPR and state privacy laws
Faces and identifiable features are blurred at the edge before any data transmission occurs. Privacy is built into the architecture, not bolted on after the fact.
That same edge architecture integrates with existing camera infrastructure via ONVIF or RTSP protocols. The primary investment is software and edge appliances—not full camera replacement—which keeps upfront costs down and speeds deployment significantly.
Behavior-Based Detection vs. Biometric Identification
Computer vision for retail loss prevention detects actions and contextual patterns, not individual identities. The system classifies behaviors:
- Concealment gestures (items moved to bags without scanning)
- Prolonged dwell at high-value fixtures
- Scan anomalies (items passing over scanners without confirmed registration)
- Cart-based loss patterns (items placed under carts or in child seats)

This is fundamentally different from facial recognition. Training datasets focus on movement trajectories, object interactions, and transaction sequences—not demographic features.
The EDPB distinguishes behavior classification (generally not Article 9 GDPR processing) from biometric templates for identification, which trigger explicit consent requirements. Behavior-based systems avoid that regulatory threshold entirely and eliminate the demographic bias risks associated with facial recognition.
Re-Identification Without Biometrics
For organized retail crime detection, computer vision can flag repeat visitors using body shape, gait patterns, and clothing characteristics across sessions—without storing facial biometric data. The system identifies that the same individual or coordinated group returned, enabling detection of theft rings and distraction-and-grab patterns that no single operator could track across camera feeds.
What Computer Vision Cannot Do
Computer vision cannot determine intent before an act occurs, and it cannot replace trained loss prevention staff. Think of it as a force multiplier: smaller teams respond faster, resources concentrate on highest-confidence events, and no one spends hours manually reviewing footage searching for incidents that may never surface.
Computer Vision Use Cases: From Theft Detection to Workplace Safety
A single modernized camera environment supports multiple retail safety functions simultaneously, distributing infrastructure costs across theft prevention, workplace safety, and operational optimization.
Shoplifting and Self-Checkout Fraud Detection
Computer vision monitors the entire self-checkout zone, not just the scanner surface. The system:
- Tracks items from the moment they enter the checkout area
- Cross-references visual item recognition with scanned barcode data in real time
- Flags mismatches—mis-scans, barcode switching, and basket-pass behaviors—as they happen
When a high-confidence anomaly is detected, staff receive discreet mobile alerts. The Forrester Total Economic Impact study of Everseen's Evercheck platform found that 75% of customers corrected scanning errors when prompted by a visual nudge on the self-checkout screen — with only 25% of flagged transactions requiring staff intervention.
That correction rate is the point. Framing alerts as customer assistance rather than accusation keeps honest shoppers unaffected while recovering real losses. Pre-deployment, 25% of self-checkout transactions contained some element of error. Post-deployment, stores recovered an average of $88,000 annually, with a less than 6-month payback period and 374% three-year ROI.
Organized Retail Crime and Perimeter Security
Organized retail crime exhibits behavioral signatures that computer vision detects across the store:
- Multiple individuals dispersing simultaneously to different high-value sections
- Repeated visits flagged through re-identification—the same body shapes and clothing patterns returning within short timeframes
- Coordinated distraction-and-grab patterns—one individual engaging staff while others act elsewhere
These patterns play out across dozens of camera feeds simultaneously — a scale no security team can monitor manually. The NRF reports that 67% of retailers saw moderate-to-significant increases in organized retail crime, with 93% of incidents in 2023 up year-over-year and violence during theft events rising 17% from 2023 to 2024. Computer vision correlates behavioral signals across feeds in real time, surfacing coordinated incidents as they develop rather than after the fact.
License plate recognition in parking lots correlates vehicle patterns with in-store incident timing, surfacing ORC activity and providing actionable intelligence for law enforcement reporting.
Retail Workplace Safety Monitoring
The same cameras monitoring for theft detect physical workplace hazards:
- Spill identification and slip-risk flagging: The system detects liquid on floors and cross-references foot traffic density to assess urgency
- Obstructed fire exits and pathways: Alerts trigger when emergency routes are blocked or merchandise creates trip hazards
- Unstable shelving and improper stocking: Visual analysis identifies leaning displays or overloaded fixtures
Computer vision also monitors employee behaviors to reduce injury risk:
- Unsafe lifting postures (bending at the waist, reaching at awkward angles)
- PPE compliance verification in applicable areas
- Continuous monitoring that safety protocols are maintained, not just checked during audits
Americold, a cold-storage operator, achieved a 77% injury reduction and $1.1 million in annual EBITDA savings using Voxel AI's workplace safety platform. Workers' compensation claims across industries dropped 23% with computer vision adoption, and hazard response times improved 65% when alerts automated detection.

Connecting Computer Vision to Your Retail Tech Stack
Computer vision delivers maximum value when integrated with existing enterprise systems, not deployed as a standalone security tool.
POS Exception Reporting Integration
By correlating video analytics with transaction data in real time, the system surfaces discrepancies before the transaction closes:
- Items visible on video but absent from the receipt
- Voids without corresponding returns
- Discount overrides inconsistent with visual context
This creates evidence-backed cases for loss prevention review rather than requiring manual investigation of thousands of transactions searching for anomalies. BizTech Magazine reports that 63% of retailers prioritize fraud and loss at checkout as a top investment area, with POS-video correlation enabling detection that neither system alone could achieve.
Workforce Management Integration
The same cameras monitoring for security events feed queue-length and foot-traffic density data to staffing systems. Managers receive alerts when checkout lines exceed thresholds or when high-traffic periods require additional floor coverage, enabling proactive scheduling adjustments.
Using security infrastructure to also optimize labor deployment means the investment case extends well beyond shrinkage reduction alone.
VMS Compatibility and Standardized APIs
That operational value is only achievable when the integration holds together technically. Well-architected computer vision platforms surface alerts within the store's existing video management system rather than requiring a separate monitoring application.
Standardized APIs push CV data directly into POS, ERP, and workforce tools — making it easier for loss prevention teams already managing multiple dashboards to adopt without disruption. The data types flowing through those connections include:
- Shelf gap alerts
- Queue depth readings
- Scan anomaly flags
Privacy, Compliance, and Avoiding Bias
Privacy architecture must be built in from the start — retrofitting it after deployment creates both technical debt and significant penalty exposure.
Privacy-by-Design Requirements
Core non-negotiables include:
- Anonymization at the edge: Faces blurred before data leaves the store environment
- Strict retention schedules with automated deletion: The EDPB recommends footage erasure within 24 hours, with storage exceeding 72 hours requiring heavy justification
- Role-based access controls: Only authorized personnel access identifiable footage, with audit logs tracking every view
Jurisdictional Regulatory Variation
Privacy regulations governing AI surveillance differ significantly by region:
GDPR (Europe):
- Article 5 mandates data minimization and purpose limitation
- Article 6(1)(f) allows legitimate interest as the legal basis for theft prevention, but requires documented past incidents
- Article 9 treats facial recognition for identification as special category processing requiring explicit consent
- Article 35 requires a Data Protection Impact Assessment (DPIA) for systematic monitoring of publicly accessible areas
US State Biometric Laws:
- Illinois BIPA: Written informed consent required before biometric collection; $1,000 per negligent violation, $5,000 per intentional violation; private right of action has generated over 1,500 lawsuits since 2019
- Texas CUBI: Notice and consent required; up to $25,000 per violation; Attorney General enforcement only
- Washington RCW 19.375: Notice, consent, or mechanism to prevent use before enrollment
The FTC banned Rite Aid from using facial recognition for 5 years (2023) after finding the retailer deployed AI-based facial recognition in hundreds of stores without reasonable safeguards. Retailers must conduct a compliance review before deployment and treat this as an infrastructure cost, not a legal formality.
Behavior-Based Detection Avoids Documented Bias
NIST tested 189 facial recognition algorithms across 18.27 million images and found false positive rates for African American and Asian faces were 10 to 100 times higher than for Caucasian faces. False positives were consistently higher for women than men.
Behavior-based computer vision—analyzing scanning patterns, item trajectories, and contextual anomalies rather than identifying individuals by appearance—sidesteps these documented biases entirely. Visible signage for customers and clear internal policies for staff are the baseline for maintaining trust in any deployment.
Building the Business Case for Retail Computer Vision
Frame the ROI argument in dual dimensions: direct loss reduction and operational gains.
Shrinkage Reduction and Loss Prevention ROI
IDC Retail Insights predicts that large retailers deploying computer vision at scale can achieve a 40% reduction in shrinkage by 2028, with 50% of large retailers expected to expand computer vision for store monitoring by that year.
The Forrester Total Economic Impact study of Everseen Evercheck (September 2024) provides independently verified ROI data:
- 374% three-year ROI
- Less than 6-month payback period
- $31.3 million net present value (for a $20 billion retailer with 200 locations)
- 0.14% revenue recovery as a percentage of total sales
- $88,000 average annual value recovered per store
- 15% reduction in loss prevention time spent at self-checkout

One US national grocery retailer interviewed for the study recovered $260,000 per location.
Operational Gains Beyond Shrinkage
The same infrastructure delivers:
- Queue optimization: Real-time foot-traffic and checkout-lane monitoring enables dynamic staffing adjustments
- Staffing efficiency: Automated monitoring reduces manual LP hours spent reviewing footage
- Reduced injury claims: Workplace safety CV achieved 77% injury reduction and 100% OSHA citation elimination in documented deployments
Phased Implementation for Multi-Site Retailers
Those operational gains make the case for expanding beyond a single pilot — but sequencing matters. Start with highest-shrink locations or highest-risk use cases (self-checkout fraud detection first, then broader safety monitoring) to generate measurable ROI before scaling across the full estate.
Codewave's QuantumAgile™ methodology supports this phased rollout — moving retailers from a validated proof of concept to full deployment without stalling on extended timelines. The ImpactIndex™ model ties project success to measurable business results (shrinkage percentages, injury claim savings, investigation time reductions) rather than delivery milestones, so vendor incentives stay aligned with client outcomes.
Software Overlay vs. Hardware Replacement
Leading computer vision platforms work with existing IP cameras via standard protocols (ONVIF, RTSP), meaning the primary investment is software and edge compute appliances — not a full camera infrastructure overhaul.
The Forrester study documents Everseen Evercheck deployment costs as follows:
- ~$1,700 per lane in capital expense
- $936 average annual cost per lane in SaaS fees
- $300,000 in annual technology savings by replacing legacy video infrastructure in some deployments
This "software overlay" approach lowers the barrier to first deployment and makes the business case easier to approve at the store level before committing to a chain-wide rollout.
Frequently Asked Questions
How does computer vision differ from traditional CCTV in retail security?
Traditional CCTV is a passive recording system reviewed after incidents occur—useful for forensics but ineffective at prevention. Computer vision actively processes live video feeds to detect and alert on suspicious behaviors in real time, turning cameras into prevention tools that enable staff intervention before losses occur.
Can AI-powered loss prevention detect theft without using facial recognition?
Yes. Behavior-based models identify concealment gestures, dwell patterns, and movement anomalies without facial identity. Repeat-visitor flagging uses body shape and clothing patterns instead of biometric data, sidestepping both regulatory triggers and the documented demographic bias in facial recognition systems.
Does computer vision work with the cameras already installed in my store?
Most AI loss prevention platforms work with standard IP cameras supporting ONVIF or RTSP protocols, requiring only edge compute appliances and software—not new camera infrastructure. This software overlay approach preserves existing hardware investments and accelerates deployment timelines.
How does computer vision help with employee workplace safety, not just theft?
Computer vision detects hazards in real time (spills, blocked exits, unstable shelving) and flags unsafe behaviors like improper lifting postures. It also verifies PPE compliance and clear emergency routes continuously, reducing injury incidents and regulatory liability on the same infrastructure used for loss prevention.
What is sweethearting, and can AI detect it?
Sweethearting is when a cashier deliberately skips scanning items for known customers. Computer vision flags it by detecting scan-to-bag ratio anomalies, unscanned items passing the register, and deviations from the cashier's normal transaction baseline.
What privacy regulations apply to using computer vision in retail stores?
Regulations vary by region. GDPR in Europe requires data minimization, purpose limitation, and DPIAs for systematic monitoring. US state laws like Illinois BIPA impose $1,000-$5,000 per violation with private right of action for biometric data. Retailers must implement anonymization, strict retention policies, and transparent disclosure as part of deployment architecture, before deployment begins.